Home » VPN Tests And Checks – The Ultimate Guide
VPN Tests And Checks - The Ultimate Guide
UPDATED May 2026
Advertising Disclosure
![]()
Many or all of the companies featured provide compensation to us. These commissions are how we maintain our free service for consumers. Compensation, along with hours of in-depth research, determines where & how companies appear on our site.
Advertising Disclosure: Many or all of the companies featured provide compensation to us. These commissions are how we maintain our free service for consumers. Compensation, along with hours of in-depth research, determines where & how companies appear on our site.
Introduction
In recent years, there has been an increase in VPN usage all around the world. People have different reasons for using VPNs. Some people use it to get access to region-specific entertainment content. In other cases, users try to access websites blocked in their regions by using VPNs.
However, many VPN users have concerns over their security and privacy over the digital world. There has been an increasing level of surveillance in some countries. While in others, VPN users can face fatal consequences if they are caught bypassing state-implemented restrictions. In the worst cases, this can be a matter of life or death for some individuals.

Therefore, many users utilize a VPN service to mask their identities. They believe by doing so, they can access the internet in a safe manner without leaking their identities. However, only a few people are aware of a little secret in the VPN industry. Unfortunately, most VPNs can leak information in certain cases.
An in-depth study of Android-free VPNs in Australia revealed something that shocked most of the VPN users worldwide. The researchers found that 84% of the tested VPNs leaked user IP address. Moreover, many experts have found that many paid VPNs are also vulnerable to dangerous traffic leaks.
Most VPN services that project themselves as complete privacy solutions are not what they claim. In fact, many of these services have the tendency to leak your IP address or DNS requests. These leaks can leave you stranded and exposed. This means the users can be put in dangerous situations depending on their location and circumstances. This revelation is especially dangerous for political dissidents or journalists in repressive countries.
Moreover, the fact that many of the VPNs have broken features adds to the concerns of users. This can be seen most often in the case of “kill switches”. Some kill switches fail to do their job and are unable to block traffic or implement IPv6 leak protection effectively. This means that your IPv6 address can still be vulnerable for leaks even after using VPNs. All it takes to expose your identity and activities is one leaked packet.
However, VPN users don’t have to worry. Not all VPNs are vulnerable to leaks. This article dictates a comprehensive guideline through which, you can detect if your VPN is suffering from leaks or not. Read along to find out about useful VPN tests and checks.
How It Works?
To understand the problem of VPN leaks further, you’ll have to have a basic understanding of how a VPN works. You see, every device on the internet has a unique ID called an IP address (you can find out your IP address through this tool). These steps explain how your basic internet connection works.
- Website addresses are displayed text form to make it easy to use for users. In turn, DNS (Domain Name Service) servers change addresses of websites from text to numeric values and save them in different folders. This allows servers to store and manage more than one websites more efficiently.
- Whenever a user tries to access a web address, your browser requires specific information to about the website. It needs the translation of the website URL into an IP address. The browser also has to know about the URL’s destination folder in that DNS server.
- Once the browser knows that, a request is passed to the DNS server. This request returns a destination for the file the browser has to load. This step is called a DNS resolution.
- The DNS server is prioritized for this job on the basis of several key factors. The OS and browser consider browser configuration, nearby DNS servers, the HOST file and Netbios, etc. to detect leaks.
- How web browsers choose DNS servers is important when discussing IP privacy and security.
When someone uses a VPN connection, the DNS resolution is taken to the servers assigned by the VPN provider. However, this doesn’t happen all the time.
It’s possible to detect the IP address from which the DNS resolution was started even when it is performed on a different server. This can expose your IP address to hackers who are eavesdropping on your network traffic through a “man-in the-middle” cyber attack.
However, you can use DNSCrypt to prevent. Still, that doesn’t guarantee your complete IP anonymity and you can fall prey to an IP leak.
EXPERT QUOTE
Connecting to a VPN before browsing the internet, should be a priority. A good VPN will encrypt your data, by redirecting your traffic to a secure tunnel, concealing your online presence from eavesdroppers and prying eyes of governments and local ISPs. Besides, a VPN will give you options to change your physical location to anywhere in the world – as long as the VPN has coverage in your target location.

Steve Ongaro
Cyber-Security and VPN Expert
How to Detect Leaks?
Before discussing the common types of leaks and the causes behind them, it’s essential to know if your system is vulnerable or not. You can run your device with several basic tests that can detect leaks in your system.

Anyone can run these tests by simply connecting to the VPN and visiting any one of many testing sites available on the internet. These websites can detect if your system is compromised and leaking your DNS traffic or IP. We’ll start with simple VPN test methods to catch apparent problems in our VPNs.
Basic VPN Tests
To detect active leaks in your system, all you have to do is to visit the website. These tests will tell you how your VPN performs when the VPN tunnel is active and stable.
You can also experiment through different test cases to see how your VPN responds to low network connectivity. Reconnecting and revaluating your VPN’s performance is also possible through this. For instance, you can:
- Connect to your VPN server and then load a testing website (such as VPmentor test) in your browser.
- Interrupt the connection manually by disconnecting it. You should do this while your VPN client is still running.
- Connect to the internet again; load some other test websites to see how your VPN performs on them. By testing on a different website you can evaluate your VPN’s performance more effectively.
Useful Test Websites
Here are some useful leak testing websites that can reveal whether your VPN is doing its job or not. You can visit any of the following to check for different tasks:
- VPNMentor(WebRTC, IPv6 leaks for VPN/TOR browsers)
- AstrillVPN
- Perfect Privacy Test Tools(IPv4 and IPv6, DNS, WebRTC leaks)
- org(IPv4 and IPv6, DNS, WebRTC leaks) – from VPN Area
- net(IPv4 and IPv6, DNS, WebRTC leaks) – from AirVPN
- test-ipv6.com(IPv4 and IPv6 leaks)
- ac(IPv4 and IPv6, DNS, WebRTC leaks, also browser fingerprinting and other things)
- com(advanced tests)
Once you’re connected to a VPN, the website should not display your real IP or DNS server. If it is doing that it’s because you have a leak.
If you’re using the VPN mentor testing tool, a blank public IP section means that your connection is safe from leaks. An example can be seen below.
However, if you were able to find leaks by any of the above testing websites, it is likely because there is some issue with your VPN.
Advanced VPN Tests
The advanced tests are not as easy as visiting a given website. These tests require technical know-how of web browsers and the functionality of other systems. However, they will help you identify any leaks your VPN is going through.
Testing Suites
The best way to identify VPN leaks is by creating a testing suite. A testing suite provides a platform to run a swarm of tests on your operating system. These tests are able to analyze traffic for leaked packets on multiple occasions.
However, creating a testing suite to read and analyze traffic is not easy. The complexity of creating test suites differs in every operating system.
A handful of VPNs have ready-to-use testing suites available to test leaks. For instance, Express VPN has one of the best testing suites to test underlying leaks in its service. These testing suites are available open-source on the VPN’s GitHub page.
Users of Express VPN can use the files provided on the above link to create testing environments for their PCs. If the users have in-depth knowledge of their operating system, they can set up these suites on Linux, Mac OS and Windows.
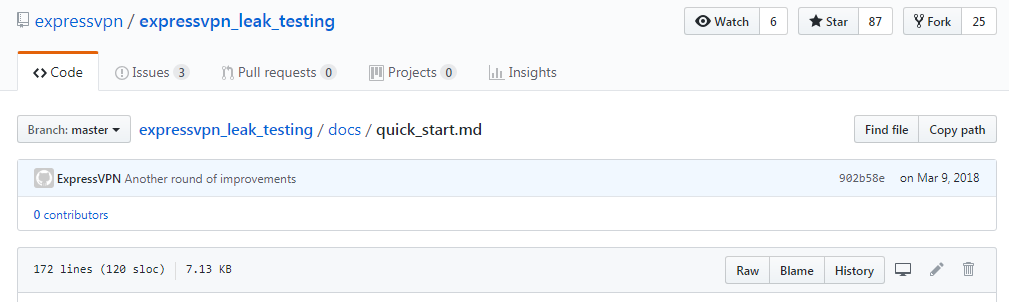
For the convenience of users, there is even a quick start guide to help them get started.
Identifying DNS Leaks
The Domain Name Server or DNS is a mechanism for converting alphanumeric URLs to numerical IPs. For instance, the DNS changes the URL “www.wikipedia.org” to 208.80.154.224 (IP value).
In the absence of a VPN, your internet service provider (ISP) is responsible for the translation process. However, this can be problematic for users that are sensitive about their online privacy. The DNS requests are clear text logs of every website the user visits while running through an ISP. ISPs can log these records and know the entire browsing history of their customers.
In places such as the US, data can be sold to third parties such as advertisers. While in Australia and the UK, legislation dictates that this data can be stored up to two years. The data is also available to authorities, who can use it for anything they like.
The DNS leak happens when the translation of URL and IPs get leaked out of the DNS tunnel. This exposes the location and IP address of your ISP, along with your browsing history. Requests going through ISPs can reveal your browsing history to whoever cares enough to tap into your system. The following websites are able to identify any DNS with the most efficiency:
· IP/DNS Leak Test at ipleak
· Perfect Privacy DNS Leak Test
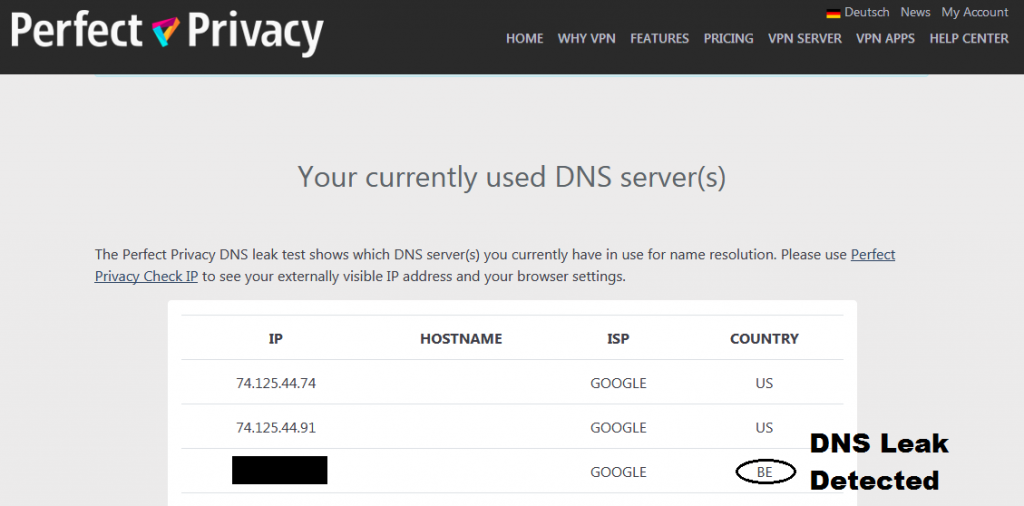
After visiting the Perfect Privacy website, we were able to detect DNS leaks in our network system. Like us, if you can see your ISP listed in the list, then you are a victim of a DNS leak too and your VPN ineffectually leaking DNS requests.
It’s easier to detect a DNS leak if you connect to a VPN server outside your own country. As you can see in the image above, there is one leak among the total of three servers.
A DNS may not expose your IP directly; however, it leaks the location and IP address of your ISP. Any average hacker can link back to you using your ISP server. Moreover, there is also the risk of your browsing history getting exposed.
Solution to DNS Leaks
You can resolve DNS leaks by using VPNs that have secure and encrypted DNS resolvers. The following VPNs claim to claim to offer DNS leak-free service to its users:
- Nord VPN (Based in Panama)
- Perfect Privacy (Based in Switzerland)
Users with in-depth knowledge can also configure DNS requests to trusted third party options manually. Wiki Leaks provides a list of alternative DNS options.
IP Address Leaks (IPv4 & IPv6)
Though IP address leaks is mainly a problem with free VPN services, paid VPN services can suffer from it too. It seldom happens with IPv6 addresses because most of these VPN services do not support this tunneling protocol.
Even premium VPNs choose to block IPv6 addresses instead of resolving the problem. However, there are VPN providers (like Perfect Privacy) that offer support to both IPv4 and IPv6 addresses. You can test IP leaks of your VPN service by visiting any of the following websites:
WebRTC leaks
WebRTC leak tests are alarming for anyone using popular web browsers such as Chrome, Opera, Firefox and even Safari. Though some VPNs offer protection against WebRTC leaks, you can’t rely on them as their performance is not as consistent as they claim.
You can use some of the testing website (such as ipleak.net) to catch IP leaks in VPNs. While testing your VPN connection for leaks, you will be able to see local address under the WebRTC section. These IPs usually start with 192.xxx or 10.xxx or even with alphanumeric IPv6 addresses that are also local.
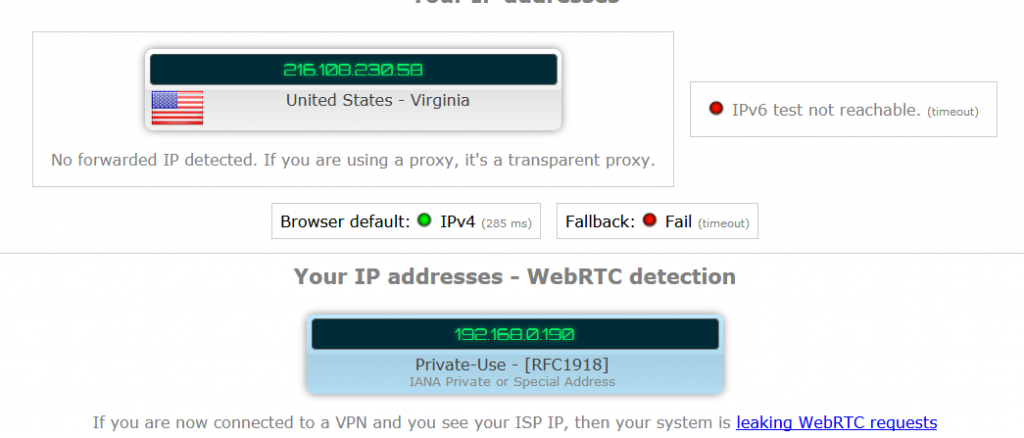
As long as the test only shows your local IP addresses, there is nothing to worry about. However, if the WebRTC section is showing your real public IP, then there is indeed a WebRTC leak in place.
VPN Speed Test
Another important test VPNs have to clear is the speed test. Using a VPN for private and secure browsing does shutter down the speed a little bit. However, if the change in speed is sizable, then it’s probably because the VPN’s server has more traffic than it can handle.
If you want to test your VPN’s speed, you can try any of the following websites:
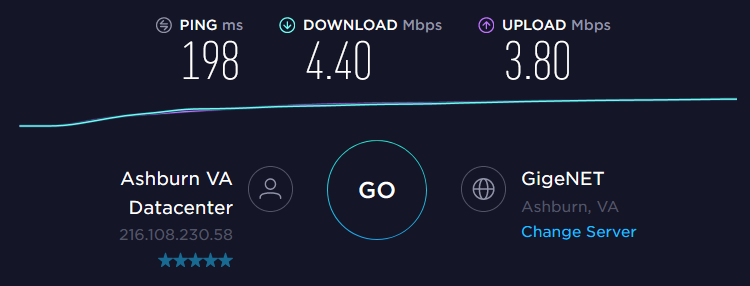
Most users operate on speeds of up to 70-100 Mbps. On a 5 Mbps internet connection, the change in speed was not as significant as you’d expect. The decrease in download speed was only 12% after switching to the VPN. This means that the connection still retained 88% of its original speed.
If you’re wondering what affects the speed of a VPN than just have to read along. The VPN speed is affected by a number of factors, some of which can be seen below:
Distance between User and the VPN
In most cases, this is the biggest factor that affects speed. The greater the distance there is between the server and the user, the lower the speed will be.
Number of Users on a Certain VPN Server
Many VPNs oversell their services and concentrate more users on a certain server than they can handle. This results in their servers getting overloaded with users. Slow speeds and dropped connections follow this event.
Regional Bandwidth Restrictions
There are many countries that have poor bandwidth infrastructure. This can limit your speed regardless of how fast your connection is. The number of people being online at a certain time in a region also has an effect on the speed of your connection. At times of high usage, connections can slow down for every user.
Internet Service Provider
Your VPN can be the fastest VPN on the planet. However, it can perform only as fast as the speed provided by your ISP. The only occasion a VPN can give faster connections than your ISP provider is when the ISP is throttling your connection for some reason.
Processing Power
Your computer is always working in the background. It also keeps on encrypting and decrypting information while you use a VPN connection. This can take sizable processing power. The faster your VPN connection is, the more power it will need while running a VPN. This means that your CPU can limit your speed if your internet speed is too much for it to handle. However, this happens on rare occasions.
How to Block Leaks?
A VPN can suffer from several kinds of leaks at once. This section of the article explains how you overcome each sort of leak.
Browser IP Leaks
One of the most common causes of IP leaks in a vulnerability found in some of the most popular browsers. This vulnerability can be exploited by hackers using WebRTC. WebRTC is a browser feature that allows web applications to function without any pre-existing plug-ins or extensions.
However, this convenience comes at a price. Popular browsers like Firefox, Chrome and Opera support WebRTC in their running. They also use STUN (Session Traversal Utilities for NAT) servers to get external network addresses. A website that maliciously wants to decode your real IP address can do so very easily by concealing a JavaScript code. This code can make UDP requests to STUN servers and redirect these requests to any web network interface it wants to.
This means that, both your actual IP address and VPN IP address can get compromised very easily. This is worrying for most VPN users as no one expects to get exposed by a piece of JavaScript code on a seemingly a harmless website.
To make it worse, the generated request is not like usual HTTP requests. They cannot get detected by the developer console, which means that browser plug-ins can’t block these requests. This can happen even if a certain browser plug-in is claiming to block these types of leaks.
However, you can resolve these issues by disabling the WebRTC in your web browser. You can do so by following the steps relevant to the web browser you use.
Disabling WebRTC in Firefox
You can disable WebRTC in Mozilla Firefox by:
- Typing in about:config in the address bar of the Firefox web browser and pressing enter.
- Clicking on “I’ll be careful, I promise” button that comes in front of you.
- Searching “media.peerconnection.enabled” in the search bar.
- Double-click the entry that comes before you. It can be seen that the value column is showing “false”.
- Ensure the safety of your Firefox browser refreshing the page.
- Enjoy your browser without WebRTC being enabled.
Disabling WebRTC in Chrome or Opera
Chrome and Opera browsers don’t have a built-in mechanism to disable WebRTC. However, some third-party add-ons/extensions are available on their respective stores. These extensions are available free of charge. They all are present on either the Opera Add-on or Chrome store pages. These add-ons/extensions claim to support the following functions:
- WebRTC Leak Prevent
- WebRTC Control
- Easy WebRTC Block
However, users with in-depth knowledge can go for options like ScriptSafe and uMatrix. By the help of these tools you can limit all other websites except the ones you absolutely trust. Still, these options are time-coning and also take up a lot of RAM. In the end, they too don’t block IP leaks, instead they block any website that attempts to know your IP address.
Disabling Web RTC in Microsoft Edge
While most the number of people that use Microsoft Edge is limited, the browser still lets you mask your real IP address. You can do that by the following two steps:
- Go to the address bar, type “about:flags” then press Enter.
- Under the label of “WebRTC”, you’ll see an option to hide your local IP over different types of connections. Click on the checkbox to activate it on the ones that you want to hide.
However, hiding your local IP address doesn’t do much in the end. You should look to try another web browser that lets you disable WebRTC altogether.
Disabling WebRTC is Safari
Apple has announced WebRTC for both Mac OS and iOS, yet there isn’t a way to disable it yet. However, Safari has strict rules when it comes to sharing device or network details with websites.
IP Leaks from VPN
Even with a VPN connection, you can’t rely on the DNS server offered by your Internet Service Provider. Your privacy remains still at risk. Users can switch to a public DNS server like the ones provided by Google. But if someone is already paying a VPN service for a secure connection, it’s useless to include a safe DNS resolution on a dedicated server.
Tunneling protocols were established so that users don’t have to access the internet using their original IPs. These protocols let users encrypt their actual IP with a public IP while using the internet. This lets them stay hidden while they browse the internet. VPNs use these tunneling protocols to mask your actual IP with a public IP.
This is why; in some cases, the culprit for your leak can be your own VPN provider. This happens when your provider doesn’t support IPv6 protocols. It’s possible that these VPN providers still use the out-fashioned IPv4 protocol.
IPv4 protocol uses a 32-bit addressing system. It can allow up to 232 devices in the world to get a unique public IP address. This may seem like a lot of devices, but the internet has been growing at an unprecedented speed. Soon the internet began to run out of these addresses and IPv6 had to be introduced. The IPv6 protocol utilized 128 bits for addressing. This means, that this protocol can support 2128 devices around the globe.
However, the adoption of this new protocol has been slow worldwide. Some major websites do support both IP protocols and also provide the appropriate channel according to the request made by the client system. The problem arises when VPN providers don’t support IPv6. They don’t even try to address the problem; instead they choose to ignore it by doing nothing at all.
Using an out-of-date VPN service provider means that you can safely access websites that support IPv6. Yet you will not be able to tunnel your requests on websites that support IPv6 protocol. This means that your request to the website will go in an unencrypted form and it will leave your IP exposed to any hacker who wants to see it.
However, you can prevent websites from exposing you to privacy risks. The following steps can help:
- Use proper firewall protocols that that block requests made outside your current VPN connection.
- Choose a VPN that gives you a dedicated DNS server and also built-in DNS leak protection.
- Choose a VPN that is compliant to IPv6 or at least offers some kind of workaround for disabling IPv6 in your OS.
- You can also disable IPv6 in your OS manually. There are many guides online on how to do so on different devices, like this one on Medium.
If you’re finding consistent DNS leaks in your VPN service, then the best way to avoid them is by changing your VPN service. You can start using a VPN that strives to remove DNS leaks. Some VPNs like NordVPN and Private Network Access claim to be leak-free.
VPNs are a great solution to establish private and secure connections over the internet. However, you shouldn’t trust them blindly. These VPNs are not without flaws. So, it’s essential to test their effectiveness on a regular basis.
DNS Leaks from the OS
People can either love or hate Microsoft products, but that doesn’t change reality itself. The vast majority of people have Microsoft Windows as their main operating system in PCs. Nevertheless, there are certain variations which you need to keep in mind while using VPNs on Windows.
As discussed before, the DNS resolution follows a priority-based hierarchical order on any operating system or web browser. The following order is followed in Windows for DNS resolution:
- The first step is the HOST file which specifies DNS mappings.
- If these files are not available at that, the OS will try to use the network-configured DNS servers.
- If that fails to resolve the URL request, the OS will send the request to the Netbios.
- In the case where the highest priority option is successful, other options are not considered by Windows OS.
This methodology was common in all Windows OS’ until Windows 10 arrived. In Windows 10, the OS sends requests to all available network adapters. Whichever DNS server responds first has the authority to direct your browser to its target web address.
In simple words, this means that using your VPN may have no effect on DNS resolution. In this case, it’s possible that DNS resolution requests will still go to your ISP server. As a result, you will be completely vulnerable when someone wants to track you through your ISP.
Another problem with using VPNs on Windows 10 is having issues with IPv6. Windows uses another tunneling method to support IPv6 addresses for users who are still on IPv4 connection. This tunneling method is known as Teredo tunneling and Windows designates it for users that lack native IPv6 support.
This means that you can leak your DNS information outside your VPN network. You can prevent this type of leak by following these steps:
- Disable Teredo Tunneling. You can do so by following the steps mentioned in this link.
- You can also disable Windows 10 optimization by turning off the smart multi-homed name resolution found in the group policy editor. Note that you don’t have the option to update group policies in the Windows 10 Home Basics version.
Protect Your Internet Browsing
GET NORD VPN NOW!

98%
OVERALL RATING

Advertising Disclosure
The information we provide you is free of charge and a result of extensive research by our product experts. We use affiliate links in our site that provide us with referral commissions. While this fact may not influence the information we provide, it may affect the positioning of this information.
